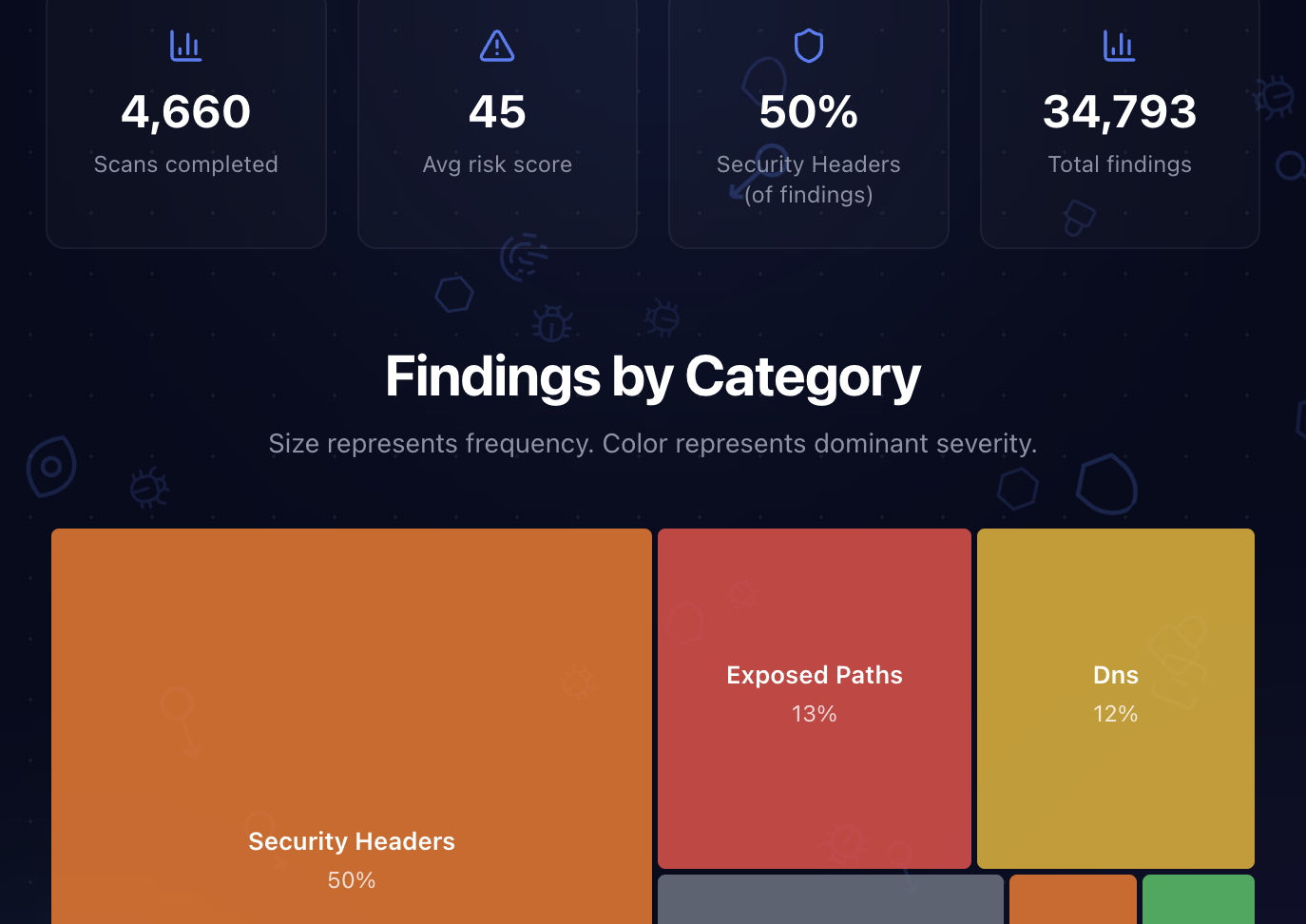
4,660 Websites, 34,793 Findings: The State of Web Security in 2026
We've now scanned over 4,660 websites with ShipShield's free security scanner and full codebase audits. That's 34,793 individual security findings across every category we check.
Instead of keeping that data locked in a database, we built a live trends dashboard that updates every hour. This post breaks down what the numbers actually mean and what you should do about it.
Source: shipshield.ai/trends
The Big Picture
Across 4,660 websites:
- 34,793 total security findings
- 45 out of 100 average risk score
- 7.5 findings per site on average
- Security headers account for 50% of all findings
That average risk score of 45 puts the typical website squarely in "not catastrophic, but definitely fixable" territory. Most sites aren't actively on fire. They're just leaving doors unlocked.
The 10 Most Common Issues
Here's what keeps showing up, ranked by how often it appears across all scans. These aren't obscure edge cases. They're security basics that most websites ship without.
security.txtmissing: 94% of sitesPermissions-Policyheader missing: 83%Content-Security-Policyheader missing: 73%Referrer-Policyheader missing: 70%X-Frame-Optionsheader missing: 62%X-Content-Type-Optionsheader missing: 55%- No DMARC record: 49%
- No SPF record: 39%
- Technology fingerprinting possible: 36%
- CORS allows all origins: 31%
Notice anything? Six of the top ten are missing security headers. And every one of them can be added in under five minutes.
If you only do one thing after reading this, add your security headers. We wrote a full guide on how to set them up.
The Category Breakdown
When we look at findings by category, the picture is stark. Security headers dominate everything else combined.

Source: shipshield.ai/trends
- Security Headers make up 50% of all findings
- Exposed Paths (like missing
security.txt): 13% - DNS (missing DMARC, SPF records): 12%
- Technology fingerprinting: 8%
- Cookies, CORS, and Server Info round out the rest
The good news: the biggest category is also the easiest to fix. Security headers are a one-time configuration change. No code refactoring, no dependency updates. Just a few lines in your web server or framework config.
How Bad Is It, Really?
Here's the severity breakdown across all 34,793 findings:
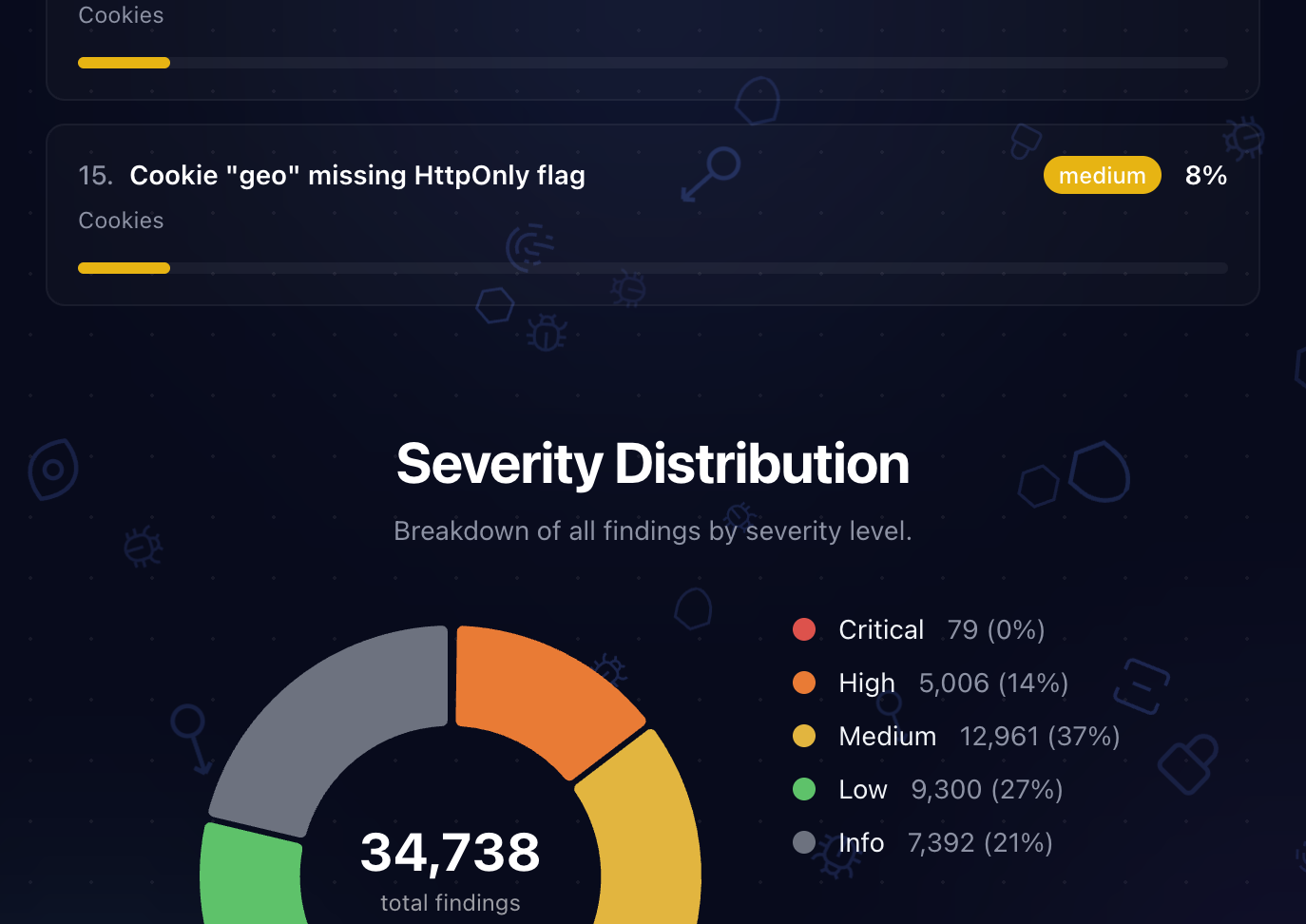
Source: shipshield.ai/trends
- Critical: 79 findings (under 1%)
- High: 5,006 findings (14%)
- Medium: 12,961 findings (37%)
- Low: 9,300 findings (27%)
- Info: 7,392 findings (21%)
The vast majority of findings are medium or low severity. That's actually encouraging. It means the web isn't riddled with critical vulnerabilities at the surface level. Most issues are configuration gaps, missing headers, and incomplete DNS records.
But don't let that calm you down too much. 14% of all findings are high severity. That's over 5,000 issues across our dataset that represent real, exploitable risks. Missing CSP headers. Missing HSTS. Things that enable cross-site scripting, clickjacking, and protocol downgrade attacks.
Security Headers: The Lowest Hanging Fruit
Security headers represent half of everything we find. Here's what that looks like by individual header:
Permissions-Policy: 83% missing (controls access to camera, microphone, geolocation)Content-Security-Policy: 73% missing (your main defence against XSS)Referrer-Policy: 70% missing (controls what URL info leaks to other sites)X-Frame-Options: 62% missing (prevents clickjacking)X-Content-Type-Options: 55% missing (stops MIME type sniffing)Strict-Transport-Security: 27% missing (forces HTTPS connections)
If you're running Next.js, here's how to add all six in one go:
// next.config.ts
const securityHeaders = [
{ key: "X-Frame-Options", value: "DENY" },
{ key: "X-Content-Type-Options", value: "nosniff" },
{ key: "Referrer-Policy", value: "strict-origin-when-cross-origin" },
{ key: "Permissions-Policy", value: "camera=(), microphone=(), geolocation=()" },
{ key: "Strict-Transport-Security", value: "max-age=63072000; includeSubDomains; preload" },
{ key: "Content-Security-Policy", value: "default-src 'self'; script-src 'self' 'unsafe-inline'" },
];
That's it. Six headers, one config block, and you've just eliminated half the findings our scanner would flag on your site.
Want to see how your headers look right now? Scan your site free. Takes about 10 seconds.
What the Free Scan Can't See
Everything in this report comes from external scanning. We check what's publicly visible: headers, DNS, cookies, exposed files, SSL, and server configuration.
But the scariest vulnerabilities aren't visible from the outside. They're hiding in your source code, your dependencies, and your infrastructure.
When we run full codebase audits, we regularly uncover:
- Leaked API keys and secrets buried in git history
- Outdated dependencies with known CVEs (some with public exploits)
- SQL injection and XSS in application code
- Missing authentication on API routes
- Docker misconfigurations like containers running as root
- Business logic flaws that automated scanners miss (we use AI review for these)
73% of security vulnerabilities hide in source code and dependencies. A surface scan tells you what's visible. A codebase audit tells you what's dangerous.
Your Security Checklist
Based on 4,660 websites and 34,793 findings, here's what to fix first:
- [ ] Add the six essential security headers (see our guide)
- [ ] Create a
/.well-known/security.txtfile - [ ] Set up SPF and DMARC records for your domain
- [ ] Remove
X-Powered-Byheaders from responses - [ ] Check your CORS policy (do you really need
Access-Control-Allow-Origin: *?) - [ ] Set
Secure,HttpOnly, andSameSiteflags on all cookies - [ ] Run a free scan to see exactly where you stand
This Data Updates Every Hour
Everything in this post is a snapshot. The real numbers keep growing as more sites get scanned. You can see the latest data at any time on our live trends dashboard. It updates automatically every hour with fresh aggregate data from all scans.
Want to see where your site falls in this dataset? Run a free scan. It takes 10 seconds, no signup required.
If the results make you nervous, a full codebase audit covers everything the free scan can't see. Source code, dependencies, secrets, infrastructure, and AI-powered business logic review. Four minutes, $25, and you'll know exactly where you stand.
Secure Your Codebase
ShipShield scans your entire codebase for vulnerabilities, misconfigurations, leaked secrets, and outdated dependencies. Get a full security audit in minutes.